You’ go through that good internet content material, extra than any other element, determines the results of your website. But what determines no matter whether or not you have prepared a good weblog report? It is not possible to say it objectively, but there are a selection of usually recognized points that can contribute to […]
[ad_1] A Java runtime environment should be able to run a compiled source code while a development kit, such as a development kit, is running. OpenJDK contains all libraries/binaries to compile and run the source code. The latter is essentially a superset of the runtime environment. More details on OpenJDK support and lifecycle can be […]
[ad_1] We proceed our Ladies in Tech Week celebration with a lot of new builders who have a huge effect at Docker – this 7 days and each and every 7 days – serving to builders create modern day day applications. Amn Rahman is a specifics engineer. You can comply with her on Twitter @amnrahman, […]
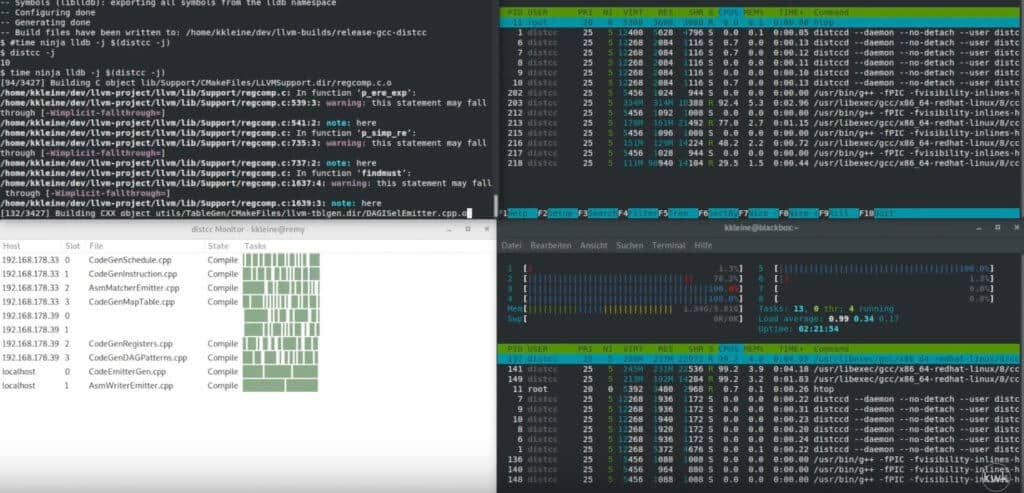
In this article, I can show you how to shorten compile time by deploying the compile load using a distcc server container. Specifically, I’ll show you how to set up and use containers running a distcc Server to distribute the compile load to a heterogeneous cluster of nodes (laptop development, legacy desktop, and Mac). […]
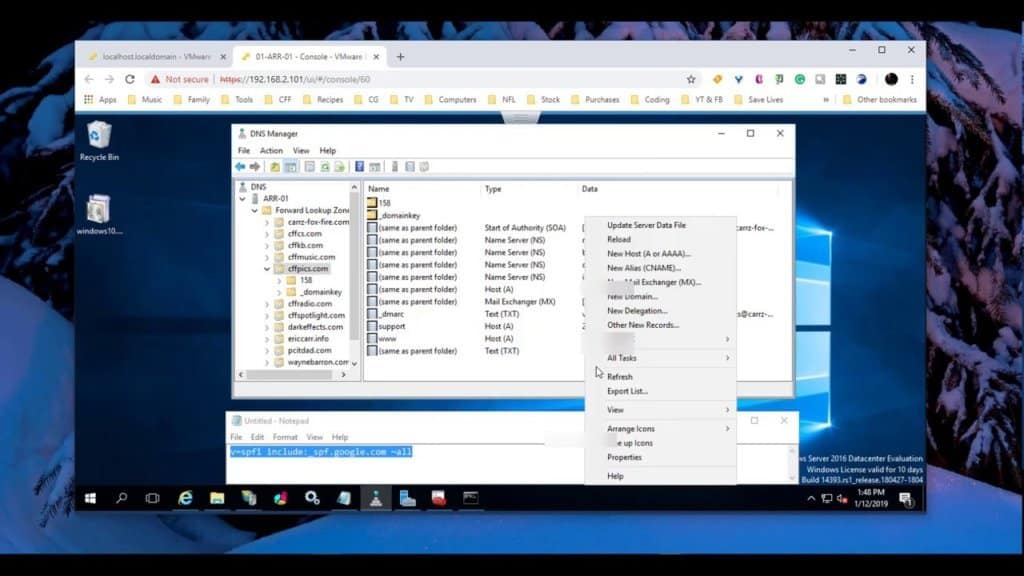
In this lesson we are gonna develop a DKIM history by our G Suite ADMIN account, we will then enter that details into our Home windows DNS (This can be finished in any DNS software that you are employing, I just happen to be applying Windows DNS Server). Then we will build the SPF file […]